
API Security: The Biggest Risk in Modern Applications
APIs have quietly become the most critical and vulnerable layer of modern application architectures. Many of today’s most damaging breaches occur without attackers ever touching a login page or user interface. Instead, they exploit assumptions baked into backend APIs - assumptions about trust, authorization, and internal access. Through real-world breach scenarios, this article explores how APIs became the new perimeter, why traditional web security models fail to protect them, and which vulnerabilities attackers exploit most often. It concludes with practical, experience-driven guidance for building effective API security into modern development workflows.
The shift of breaches to API endpoints
What would happen if an attacker never touched your login page, never rendered your UI, and still walked away with your most sensitive customer data? That question stopped being hypothetical years ago. A growing number of high-impact breaches now begin and end at a single API endpoint, often one that engineering teams assumed was “internal” “low risk” or protected simply because authentication was in place.
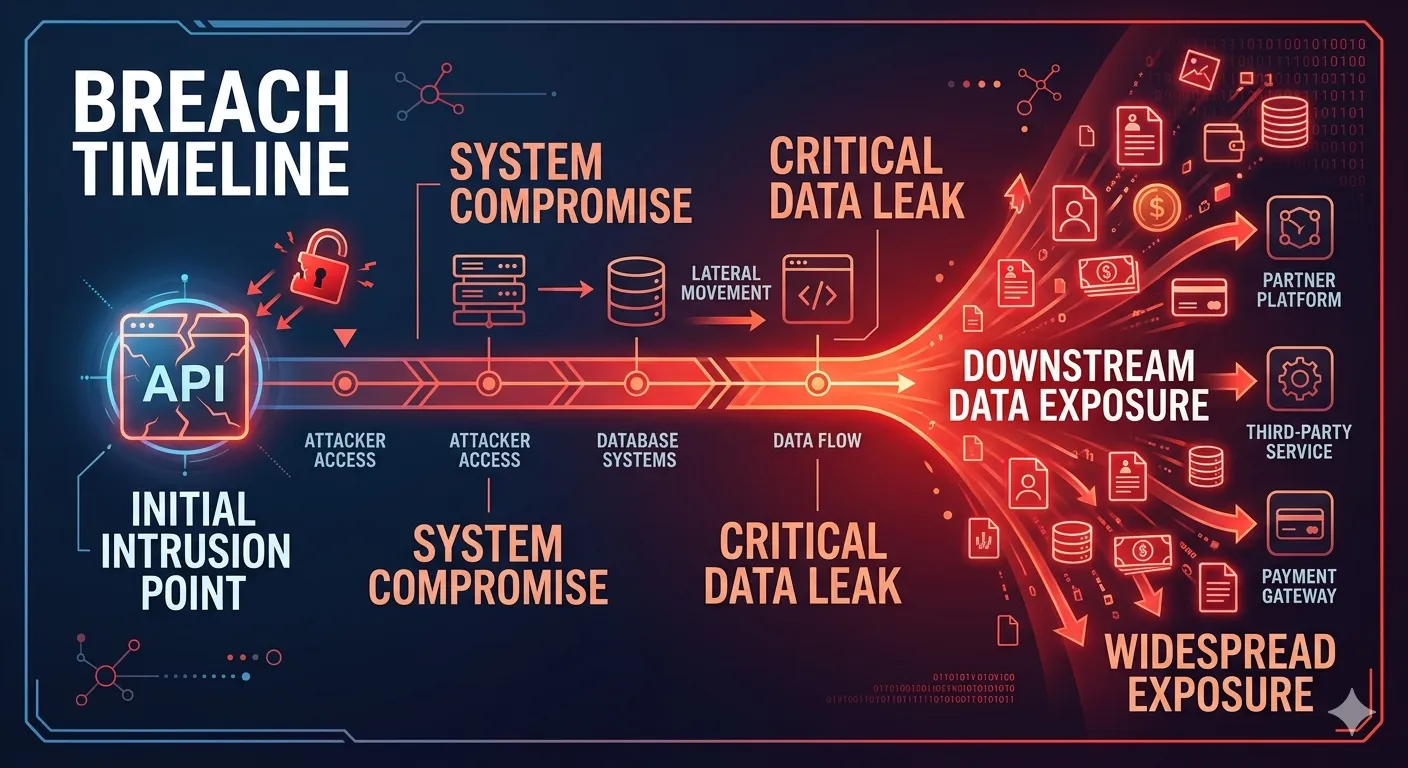
A recent incidents in the fintech sector illustrates the problem clearly. Attackers discovered an undocumented REST endpoint used by a mobile app to retrieve transaction histories. By changing a numeric account_id value in the request, they accessed millions of financial records across tenants. No cross-site scripting, no SQL injection, no browser exploitation. Just a valid token and a predictable API call. The result included regulatory investigations, emergency API shutdowns, and weeks of customer trust erosion. Industry data from multiple breach reports consistently shows APIs and backend services playing a direct role in over half of modern application compromises, particularly in cloud-native environments.
The emotional and business impact is immediate. Legal teams scramble to assess breach notification requirements. Engineering halts feature work to triage exposure. Customers abandon platforms that fail to protect their data. What makes these incidents especially painful is that many organizations invested heavily in traditional web security controls that simply never engaged.
This article explains how application architecture quietly shifted the security perimeter from browsers to APIs, why traditional web security models no longer map to that reality, which API-specific vulnerabilities drive real breaches, and how attackers actually test and exploit APIs in practice. It closes with concrete, experience-driven guidance on embedding API security into modern development lifecycles without grinding delivery to a halt.
The Rise of APIs as the new application perimeter
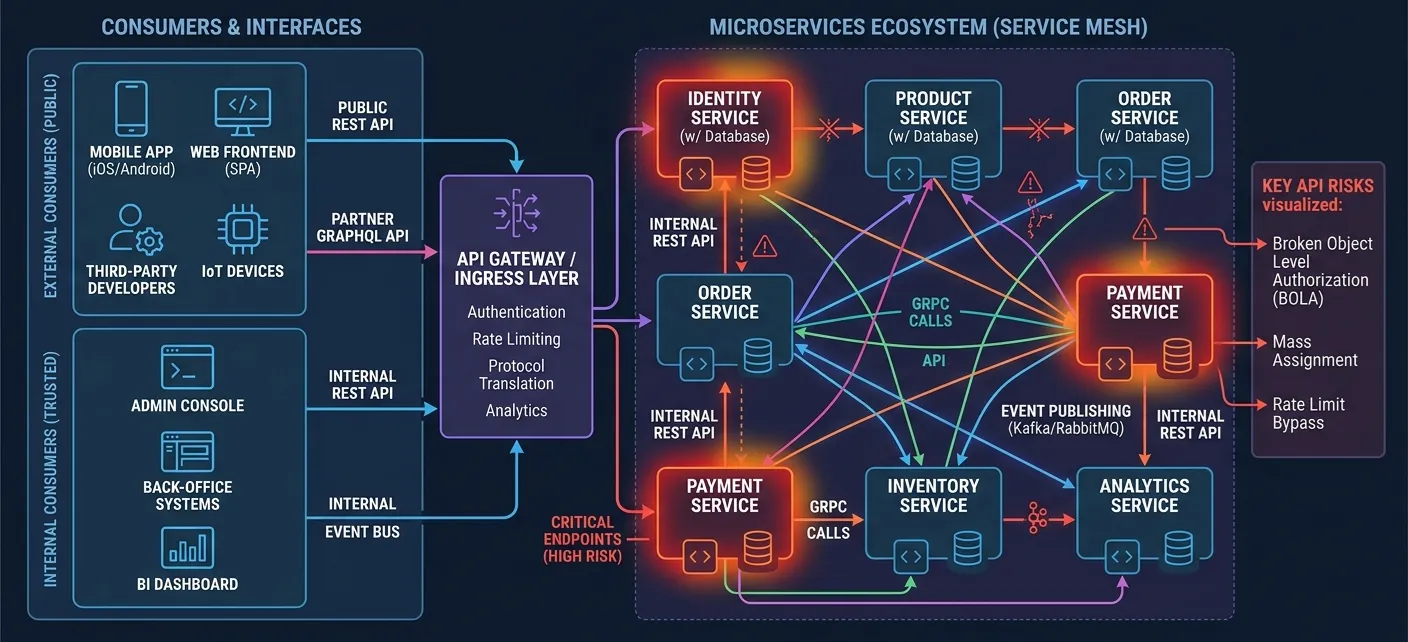
When did APIs stop being plumbing and start becoming the front door to the business? The answer lies in how modern systems are built. Over the last decade, organizations dismantled monolithic applications into microservices, embraced cloud-native platforms, and shipped mobile-first and SaaS products that rarely render HTML on the server. Each of those shifts replaced server-rendered pages with APIs that directly execute business logic.
In a typical e-commerce or fintech platform today, dozens of services communicate over REST, GraphQL, gRPC, events, and webhooks. A single customer action may trigger synchronous REST calls to user-profile and payment APIs, asynchronous events on Kafka 3.x topics, and outbound webhooks to fraud or notification providers. Internal east-west traffic inside Kubernetes 1.28 clusters often dwarfs north-south traffic from the internet, yet those internal APIs frequently handle the most sensitive decisions.
This architectural shift quietly moved authorization logic, pricing rules, eligibility checks, and data access controls into APIs. They are no longer thin data pipes. They are the application. That reality turns old assumptions about “internal trust” into a liability. Historically, services inside a VPC or cluster shared credentials or skipped authorization entirely, assuming perimeter defenses were enough. Once an attacker compromises a single pod, container image, or CI service account, that implicit trust enables lateral movement at API speed.
Consider an internal admin API that was never intended to be exposed externally. It listens on a cluster-internal address and accepts a shared API key. An attacker who steals that key from logs or environment variables can now enumerate users, reset credentials, or disable controls across the platform. Zero trust principles exist precisely to counter this assumption, requiring explicit authentication and authorization on every call, regardless of network location.
The risk compounds when third-party, mobile, and partner APIs enter the picture. Public APIs consumed by mobile apps, JavaScript SDKs, and business partners multiply exposure beyond direct organizational control. Inconsistent OAuth 2.0 scope enforcement, over-permissive tokens, and weak monitoring of partner usage are common. A recurring pattern involves partner APIs offering broader permissions than the web UI ever exposes.
The attack surface expansion is stark when compared to monolithic apps. What used to be a login page and a handful of routes becomes hundreds of endpoints across versions like /api/v1, /api/v2, /beta, and /internal. Deprecated APIs linger for years. Feature flags keep half-finished logic reachable. Each endpoint, method, and version becomes a durable target.
Traditional web security models no longer work
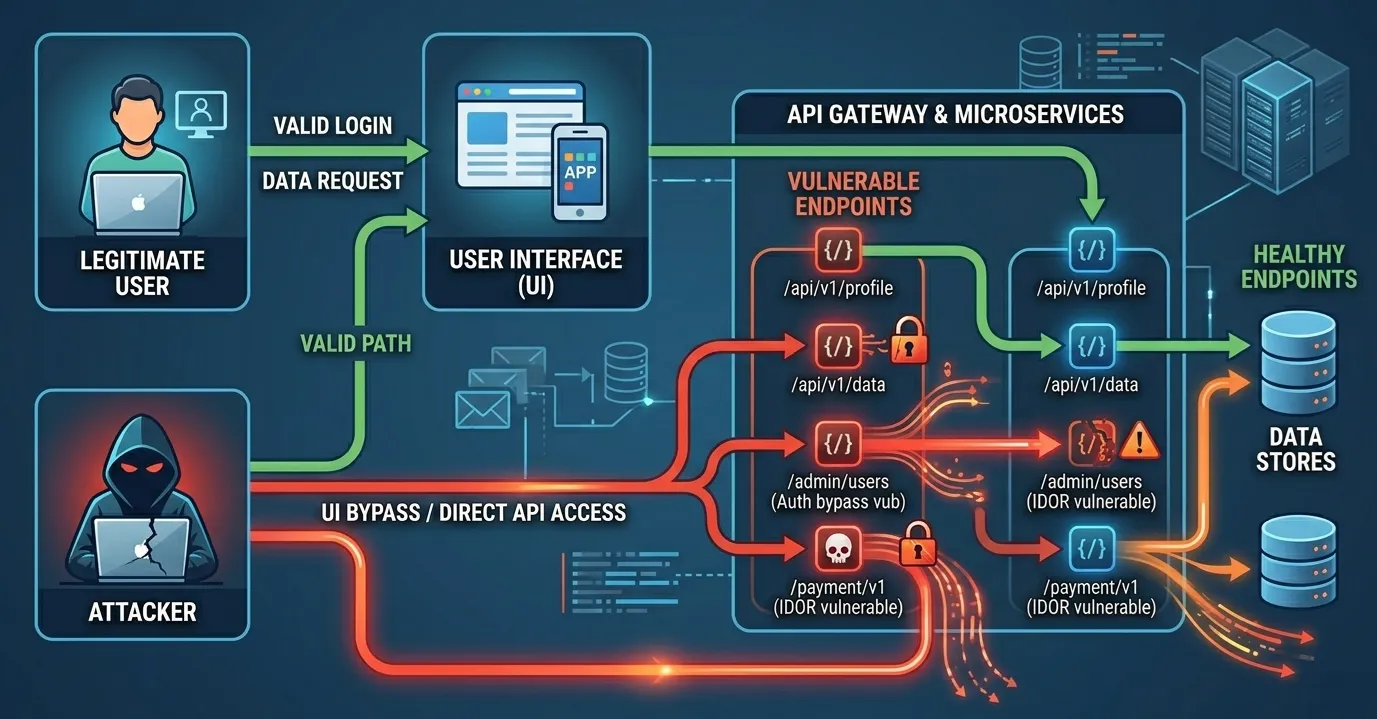
Why do teams with strong web security still lose data through APIs? The root cause is a mismatch between assumptions and reality. Classic web security models were built around browsers, forms, sessions, and user-driven flows. APIs operate under entirely different constraints.
Traditional OWASP Top 10 web risks focus heavily on cross-site scripting, CSRF, and clickjacking. Those threats assume a browser executing untrusted code. Pure APIs consume JSON over HTTP, use stateless token-based authentication, and have no DOM to exploit. As a result, defenses optimized for the browser never engage. Instead, authorization failures, data exposure, and logic flaws dominate.
Attackers take advantage by bypassing the frontend entirely. Mobile apps are reverse-engineered using tools like jadx or Frida. JavaScript bundles reveal endpoint names. OpenAPI specs leak through developer portals. Once discovered, APIs are called directly using curl, Postman, or Burp Suite Professional. Frontend validation, disabled buttons, and hidden fields provide zero protection.
A simple example illustrates the point. A web UI restricts users from exporting more than 100 records. The API endpoint accepts a limit parameter without server-side enforcement. An attacker runs:
`curl -H "Authorization: Bearer eyJhbGciOi..." "https://api.example.com/v1/orders?limit=100000"`
The API responds with the full dataset because the UI constraint was never enforced in backend logic.
Authentication adds another layer of misunderstanding. Proving identity with a JWT compliant with RFC 7519 does not define what that identity can access. Many breaches involve valid tokens reused to access unauthorized resources. Claims like sub, scope, and aud must be evaluated consistently. A user token scoped for “orders:read” accessing another user’s orders is a broken authorization problem, not an authentication failure.
Machine-to-machine communication amplifies the challenge. Service accounts using OAuth 2.0 client credentials, long-lived API keys, or mutual TLS often lack fine-grained context. Tokens end up embedded in CI/CD logs or container images. Once leaked, they grant broad access with no user-level constraints.
API-specific vulnerabilities that drive real breaches
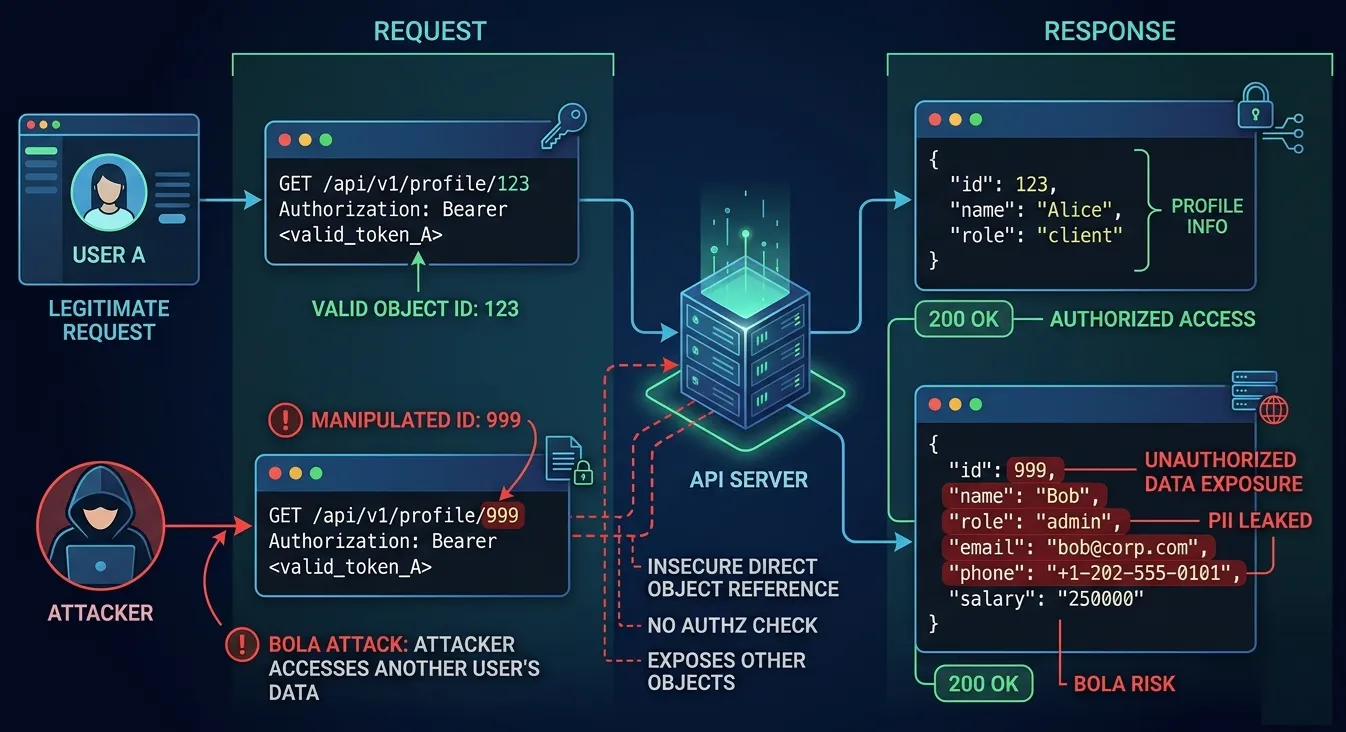
Which flaws actually matter in practice? Incident data consistently points to a small set of API-specific vulnerabilities causing outsized damage. At the top of the list is Broken Object Level Authorization (BOLA).
BOLA occurs when an API exposes object identifiers in URLs, query parameters, or JSON bodies and fails to verify ownership. An endpoint like GET /api/v1/accounts/12345 assumes the caller owns that account. Attackers change the ID and retrieve someone else’s data. The exploitation flow is trivial and devastating.
Consider a request:
`GET /api/v1/orders/781234`
The response includes another customer’s order details because the API only checked that the token was valid, not that the order belonged to the caller.
Broken Function Level Authorization follows closely. UI-based role enforcement hides admin actions, but APIs fail to enforce roles server-side. A standard user calls POST /api/v1/admin/refund and the backend executes it. Role-based access control and attribute-based access control must be enforced consistently at the endpoint.
Excessive data exposure and mass assignment stem from convenience-driven development. Frameworks like Spring Boot or Rails automatically serialize ORM objects. APIs return internal fields like is_admin, credit_limit, or password_reset_token because no explicit response schema exists. Mass assignment allows attackers to inject fields such as "role":"admin" into JSON payloads during object creation.
Rate limiting failures enable enumeration and scraping. Without limits, attackers paginate through entire datasets. Token misuse compounds the issue when expiration, audience, or scope checks are skipped. A single leaked token can fuel hours of automated extraction.
Why APIs are harder to test and secure
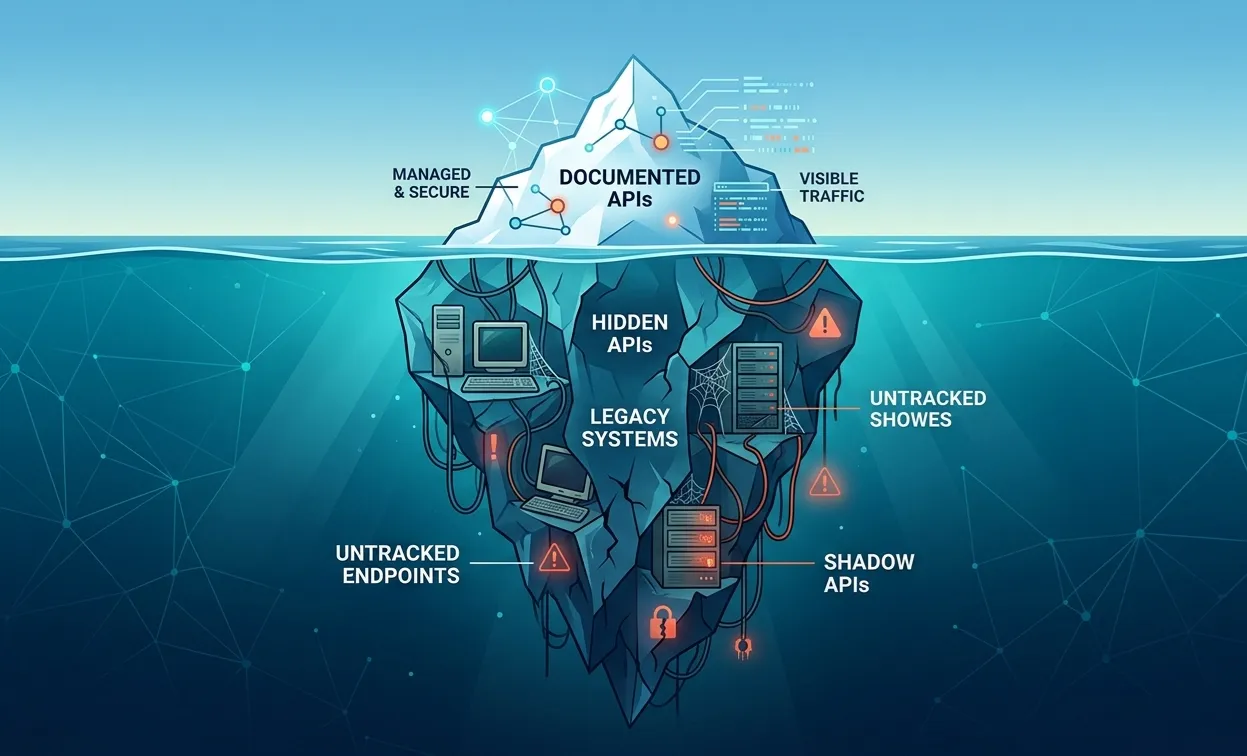
If these issues are well-known, why do they persist? One answer is visibility. Most organizations lack a complete API inventory. Shadow APIs emerge from deprecated mobile apps, internal tools, and experiments that quietly became production. A forgotten /api/v1 endpoint remains accessible years after v3 launched.
Version sprawl makes the problem worse. Authorization logic is copied across services and versions. A fix lands in v2 but v1 remains vulnerable. Security debt compounds as teams scale. Testing machine-to-machine flows adds complexity. Cron jobs, event-driven consumers, and webhooks lack UIs and require careful simulation of service identities.
A common example involves webhooks that trust incoming requests without signature verification. An attacker sends crafted POST requests to trigger internal workflows. Without proper validation, the system executes unauthenticated actions.
Organizational silos exacerbate the issue. Developers own endpoints, platform teams manage gateways, security teams define policies, and partners consume APIs. Without shared threat models and clear accountability, gaps persist.
How pentesters actually test APIs
Understanding offesive security methodology turns abstract risk into actionable defense. Attackers begin with API discovery. They inspect mobile apps, browser dev tools, leaked OpenAPI files, and predictable patterns like /users, /accounts, and /admin. Tools such as Burp Suite, Postman, and mitmproxy automate request replay and modification.
Next comes schema analysis. JSON responses reveal relationships. Attackers fuzz object IDs, nested attributes, and optional fields. A deeply nested field like "owner_id" becomes a pivot point. Business logic abuse follows. Legitimate calls are chained to violate invariants, such as creating a resource, reassigning ownership, then invoking a restricted action.
A simplified comparison highlights the difference between vulnerable and secure logic:
Insecure: `if token.valid(): return order`
Secure: `if token.valid() and order.owner_id == token.sub: return order`
This explicit ownership check blocks entire classes of attacks.
Building API security into the development lifecycle
API security becomes manageable when embedded early. Design-time threat modeling identifies resources, actors, and trust boundaries. Teams can ask:
- Which objects does this API expose?
- Who should access each action?
- What data is sensitive or regulated?
- What assumptions exist about internal trust?
A lightweight threat model for a CRUD API often reveals BOLA risks immediately.
Automation reinforces discipline. CI/CD pipelines validate requests and responses against OpenAPI schemas. Tests assert that unauthorized object access fails. Builds break on critical issues. Manual testing remains essential for business logic flaws, scheduled before launches and major refactors.
Consistency matters. Centralized authorization libraries, policy engines, or gateways enforce uniform checks. Logging and monitoring focus on high-risk endpoints first. A risk-based remediation approach prioritizes APIs handling payments, identity, or bulk data.
A practical checklist helps teams start:
- Inventory all APIs, including internal and legacy
- Test every endpoint for object ownership enforcement
- Validate request and response schemas explicitly
- Enforce rate limits and token expiration
- Review service account scopes quarterly
Conclusion
APIs now define the real attack surface of modern applications. They expose business logic directly, operate beyond the browser, and fail loudly when traditional security models are applied blindly. Breaches driven by BOLA, broken authorization, and data exposure are predictable outcomes of today’s architectures.
- Inventory APIs immediately and include internal, partner, and deprecated endpoints.
- Prioritize testing for object-level and function-level authorization using tools like Burp Suite.
- Integrate API threat modeling and testing into the SDLC as a standard practice, not a post-incident reaction.
The path forward is clear. Start with simple ownership checks and schema validation. Build consistency through shared libraries and automation. Review APIs with the same rigor attackers already apply. The question is no longer whether APIs will be targeted, but whether defenses will be in place when they are.
Related Posts
All postsGet your three regular assessments for free now!
- All available job profiles included
- Start assessing your candidates' skills right away
- No time restrictions - register now, use your free assessments later
- All available job profiles included
- Start assessing your candidates' skills right away
- No time restrictions - register now, use your free assessments later


